Comprehensive
Penetration Testing
Tailored for
Boutique Penetration Testing
With 15 years of experience and hundreds of projects behind us, we’ve developed a boutique approach to penetration testing. We work on one project at a time to go deep, focus fully, and find the critical security issues that could seriously impact your business.
one dedicated team
Your assessment is handled by a focused team
with no parallel assignments, ensuring deep
attention and complete alignment with your
security objectives.
beyond the scope
If critical risks emerge outside the original scope,
we escalate and investigate — because
business threats rarely stay confined
to a predefined boundary.

exploitable risks
prioritize vulnerabilities with real-world impact —
those that could lead to data breaches, financial
loss, or compliance violations.
the engagement. You’ll always have direct access
to senior consultants, ensuring full visibility
and rapid response.
verification included
of remediated findings, helping your team confirm
fixes and strengthen your overall security posture.
and industry recognition
HITB, and top CTF competitions,
backed by OSCP-certified professionals.

and zero-day discovery
over 12 previously unknown (0-day) vulnerabilities
during client engagements.
stack, application architecture, and business logic
to identify high-impact risks.
Mobile, Infrastructure, and API security —
where real threats live
ONSEC.io Team
- OSCP certified experts
- 63 years overall team seniority
- F500, NASDAQ, unicorn as well as start-ups customers
- API, web apps, mobile, network & cloud infrastructure pentests and security audits
- Security awareness and anti-phishing trainings
- 30+ researches published
- Black Hat, HITB, BSides speakers
- CTF competitions winners
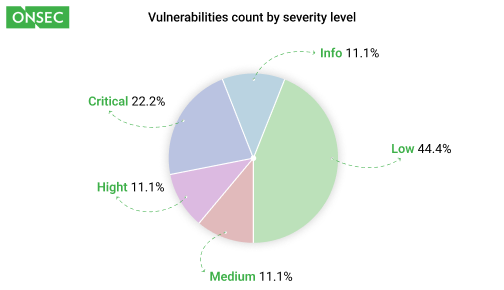
Inside ONSEC’s Pentest Report
in depth of analysis, focus on business-critical risks, and clarity of remediation guidance.
ONSEC reports are designed to support real-world security decisions —
not just check compliance boxes.
Industries
- Required by PCI DSS, SOC 2, AMLD, DORA, and other strict financial compliance frameworks
- Focused on business logic abuse: transactions, payouts, rate manipulation, and fund diversion
- Simulates user-centric threats: credential stuffing, client-side exploits, and API abuse at scale
From Revolut’s data breach to Robinhood’s support system hack—financial platforms bleed fast and publicly.
Pentesting isn’t optional in fintech—it’s margin protection in disguise.

- Targets of constant attack: from account takeovers to game rigging and payment fraud
- Aligned with UKGC, UIGEA, AML, and other global betting regulations
- Includes deep white-box audits of third-party platforms and white-labeled
iGaming platforms are goldmines for attackers—pentesting keeps the odds in your favor.
Average breach cost? $10M. One hidden flaw can take down your license.
- Attackers target cheats, dupes, account takeovers,
and in-game economy exploits - Covers compliance: GDPR, AMLD, DORA, PCI DSS — yes,
even game studios are in scope - Finds token abuse, currency inflation paths, and real-money trading backdoors
From EA account hijacks to Diablo gold dupes, the industry’s been burned.
Pentesting ensures your game isn’t next.
- Attackers hunt for broken auth, tenant leaks, and privilege escalation paths in multi-user environments
- Covers SOC 2, ISO 27001, GDPR, and rising enterprise demands for pentest reports in procurement
- Simulates real-world SaaS risks: session hijacks, forgotten admin panels, and CI/CD misconfigurations
From Slack’s private GitHub leak to Okta’s support portal breach—SaaS is always in the spotlight.
Pentesting shows customers you take trust seriously —before they ask.

- High-value targets for credential theft, code tampering, insecure data storage, and platform-specific bypasses
- Threat actors exploit overlooked client-side flaws to gain access to sensitive data and user sessions
- Pentesting identifies vulnerabilities that lead to fraud, reputational risk, and app store delisting
Business Value: Reduces breach risk in mobile channels, ensures platform compliance (App Store, Play Store),
and protects brand trust where most users engage.

- Core of digital business operations, frequently exposed to authentication flaws, API chaining abuse, and business logic manipulation
- Pentesting simulates full attacker workflows across UI and API surfaces to reveal real-world exploitation paths
- Focus on uncovering hidden vulnerabilities that impact revenue flow, user integrity, and data confidentiality
Business Value: Protects critical revenue-generating services, accelerates enterprise sales (SOC 2 / ISO 27001 alignment), and reduces incident response costs.
- Prone to misconfigured access controls, exposed cloud assets, and lateral movement inside virtual networks
- Attackers exploit these paths to access production data
or disrupt services through privilege escalation - Pentesting validates cloud hardening efforts, helping prioritize high-impact misconfigurations and policy enforcement gaps
Business Value: Prevents costly outages and data leaks, validates ROI from cloud security tooling, and strengthens board-level trust in infrastructure governance.
- Exposed to prompt injection, tool misuse, training data leaks, and automated misuse scenarios
- Pentesting uncovers logic and workflow manipulation
that could lead to sensitive output leakage, compliance violations, or autonomous execution abuse - Targets both user-facing GenAI interfaces and backend
AI agent ecosystems
Business Value: Ensures safe AI rollout at scale, enables regulatory alignment (AI Act, GDPR), and safeguards innovation pipelines against emerging AI-specific threats.